Alaska Air Group and a 4 Year Leak
What Happens When a $4.5bn Airline Loses Control of it’s $12bn Asset
SEE THE MAIN REPORT HERE
20 March 2026 | noseyparker.org
DISCLAIMER: The author holds a short position in Alaska Air Group (ALK) and stands to profit from a decline in the share price. This document should be read in conjunction with the main report dated 18 March 2026. It represents analysis of publicly available information and constitutes opinion, not investment advice.
ALK has known since at least 2022 that its loyalty platform has a critical cyber vulnerability.
Thousands of its most loyal and lucrative customers have had their accounts drained by hackers. Alaska’s consistent response is to blame the victim’s password hygiene, restore the stolen points as a “one time courtesy,” and permanently restrict the victim’s account.
Today the exact unremediated vulnerability is unveiled, along with the organised crime money trail that surrounds it.
For investors, the loyalty programme -- valued by management in December 2024 at $12 billion -- has lost its financial controls as a result of this flaw.
The main report released simultaneously today should be consulted for evidentiary precision and sourced evidence. What follows is a precis of that investigation.
I shall start with repeating the spark of this all.
Act 1: The LinkedIn Spark
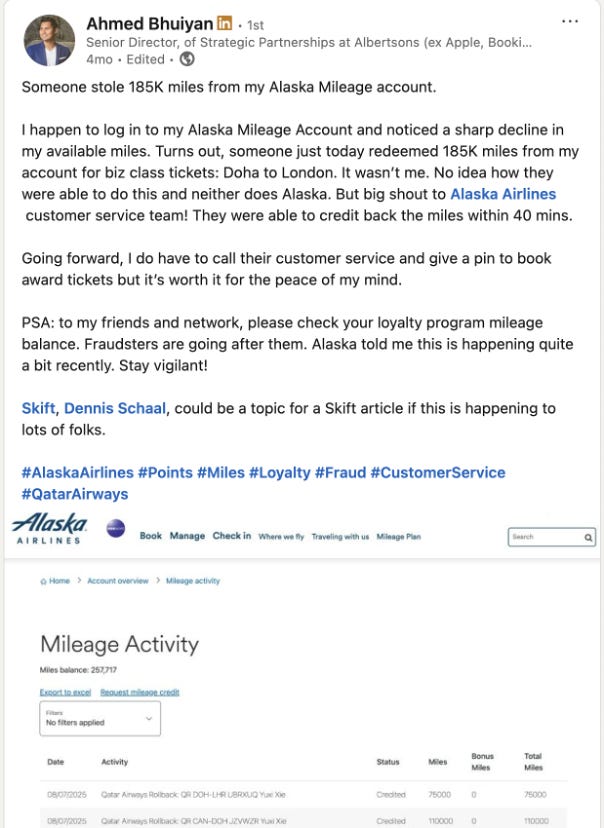
In August 2025, the author saw a LinkedIn post about an Alaska Airlines member having his account drained of loyalty points and subsequently replenished. Others responded to report the same experience.
Three questions in this posting bothered the author:
Why can Alaska not block these clearly fraudulent bookings and stop the thefts?
What purpose could the mandatory telephone PIN booking system, forced upon the victim, serve?
Why would the fraudulent traveller take the staggering risk of passing through the most secure environments conceivable, under his real identity, for a few transient hours of comfort?
The questions were perplexing enough to launch an investigation.
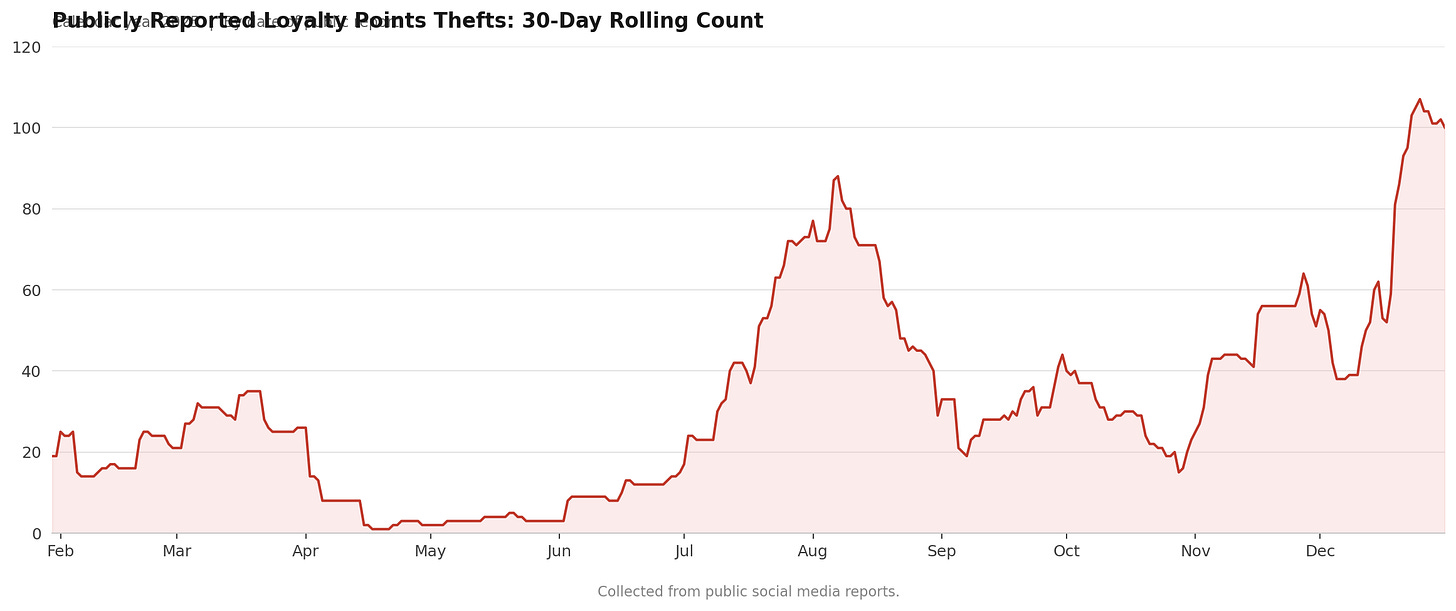
Act 2: 425 Thefts Gathered
The investigation found 425 victims. Each sourced and archived.
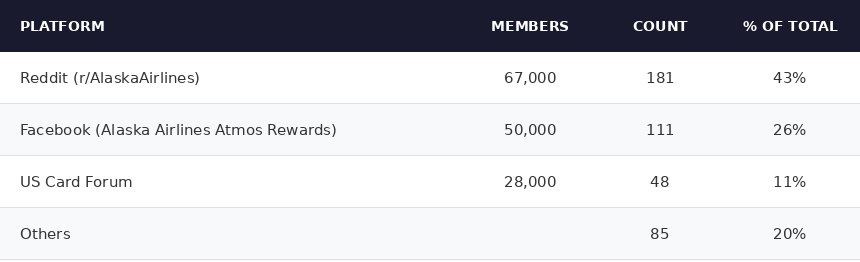
The cases were found predominantly in niche special interest forums:
About 30% shared the quantum of their loss. The average was approximately 220,000 miles.
Act 3: Mode of Theft
The thefts almost universally displayed the same characteristics. The pattern has been consistent since 2022:
Accounts were compromised to book flights within days of travel.
Flights were on partner airlines.
Members’ notification emails were suppressed.
In 96% of cases, the victim discovered the theft by reviewing their own account, and then informed Alaska.
Act 4: Alaska’s Response Policy
Alaska’s responses were so consistent that they must be the product of a policy, also unchanged since 2022.
Alaska reimburses the stolen points as a “one time courtesy.” This language leaves the victim in no doubt who Alaska blames.
Victims are then barred from booking award travel online. They must telephone Alaska, verbally relay a PIN, which unlocks their account for online booking for one hour.
Act 5: The Industry Backdrop
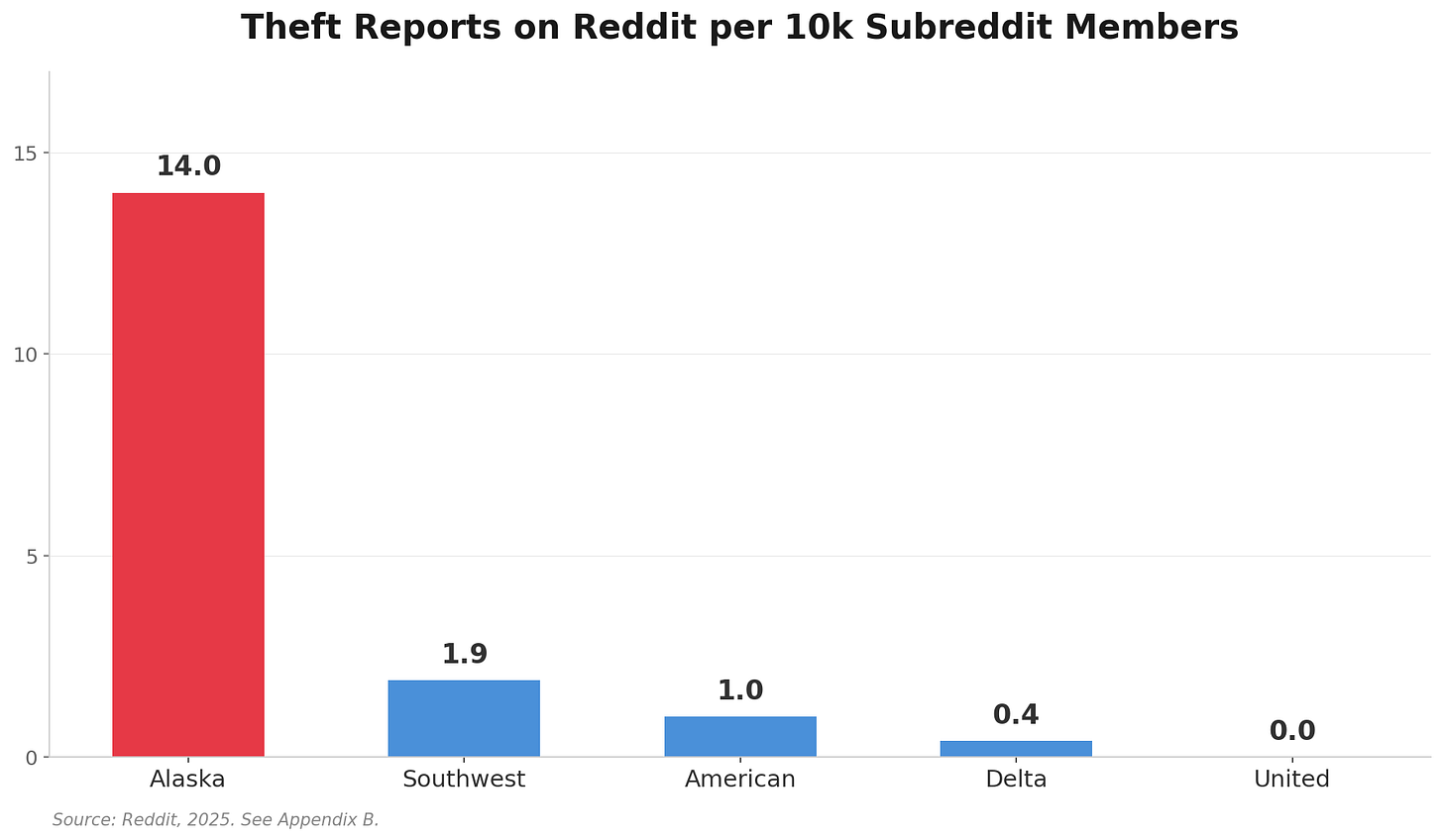
A snapshot was taken with controlled search terms to confirm what a cursory internet search shows indisputably: Alaska is suffering from loyalty account theft at a rate unmatched by any peer airline.
`
Act 6: Tip of an Iceberg
The 425 victims are indisputably a fraction of the actual total. Few people post publicly about a largely remediated matter that carries some embarrassment.
The USCardForum.com statistics were striking. A Chinese-language forum with 12,000 weekly visitors, where fewer than 5% of posts relate to Alaska, produced 48 victims willing to come forward. Extrapolations are not definitive, but hacked accounts in 2025 are indisputably in the thousands.
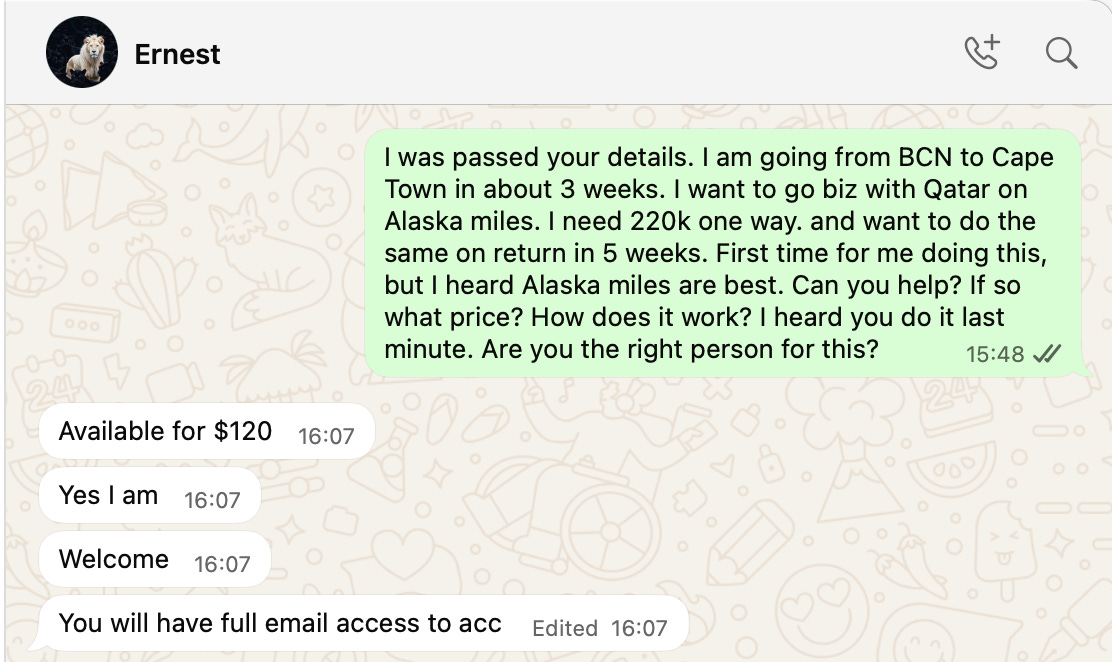
Act 7: The Criminal Marketplace
The miles are sold for extraordinary prices on the black market.
To take an admittedly extreme example: a $35,000 family-of-four trip to Barcelona can be had for less than $200.
The main report offers a host of insights from six sellers identified during the investigation (though their integrity must be in question). All were found with a Google search that located them openly on Facebook.
Highlights:
“Ernest” only sells accounts that have been dormant for more than three years.
“Akis” has an inventory of 3,000 accounts ready to go.
“Asad” says his six-man operation sells 50 to 60 Alaska accounts a week.
The revelation of their respective payment coordinates took the investigation upon a new path.
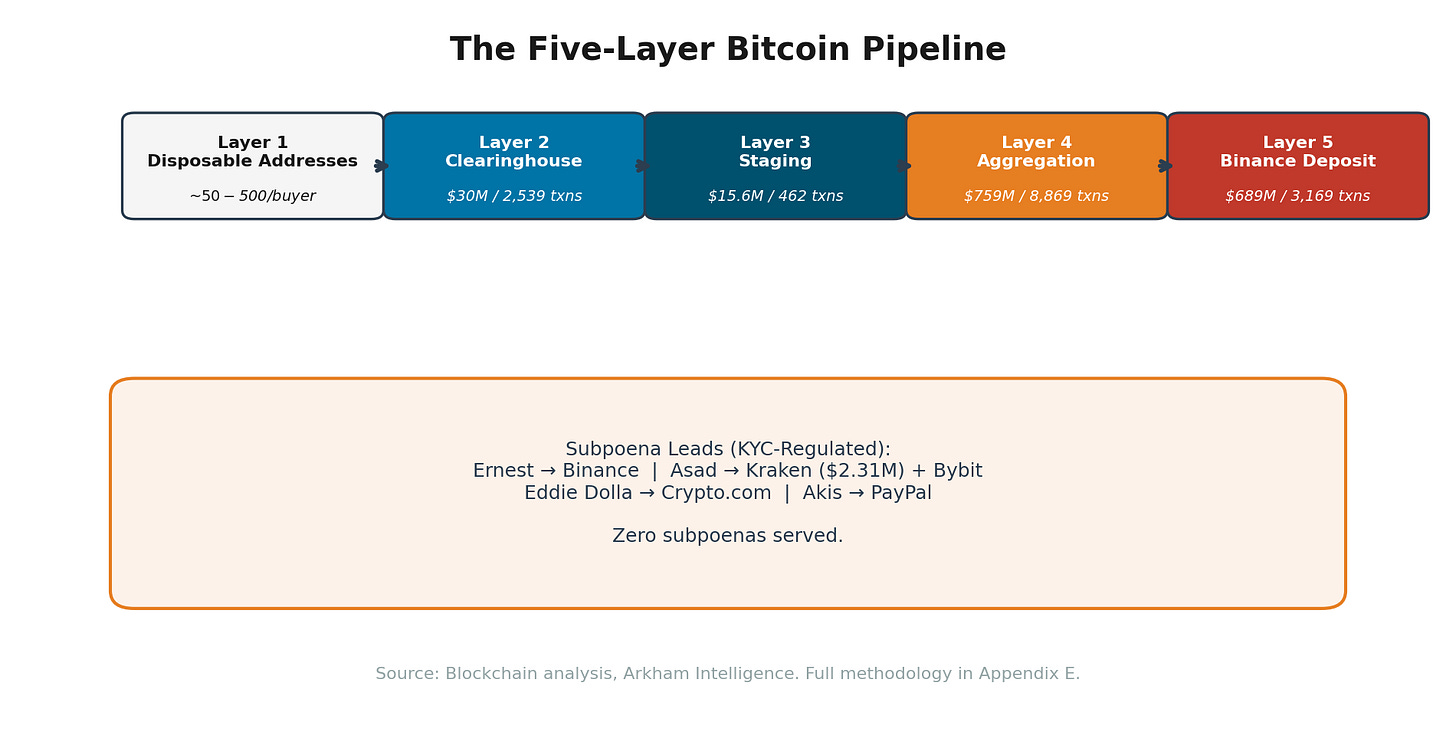
Act 8: The Money Trail
The various ETH and BTC wallets proffered for payment opened a new thread. Some went straight to exchanges. Others entered a river of apparent illicit capital. Two addresses connected with accounts through which over $759 million has flowed to KYC-regulated exchanges.
This entire network appears to be a flurry of subpoenas away from dismantlement. The lack of caution suggests the impunity under which these operators work.
Act 9: Law Enforcement
Instinctively, one would expect an airline beset by attacks of this nature to pour resources into facilitating arrests and publicise them widely as a deterrent. Victim accounts suggest the opposite.
The State of Alaska Attorney General recently challenged Alaska on its reticence to assist law enforcement. Generously, one could call it discretion.
[IMAGE PLACEHOLDER: AG letter excerpt]
Act 10: A Track Record of Discretion
The main report details half a dozen instances in Alaska’s filings where management reveals a notable predilection against disclosure. The subject of hacked member accounts has been met with the same silence.
There is no doubt management are aware of these thefts. The VP of Loyalty stated specifically that this had “visibility all the way up to our CEO.” The local press at Fox, Kiro7, and the Seattle Times have separately investigated this matter.
If it is implausible that management has no awareness of the thefts, it is equally implausible that they have no awareness of the PIN lock system that follows an account compromise. The encumbrance on their most loyal customers is such that the CEO must have asked questions, and the additional cost must have drawn the CFO’s attention.
Act 11: The Riddle of the PIN Lock
Yet there it remains. Why?
Consider the established customer service policy after a theft. Miles are restored as a “one time courtesy.” Those very words attribute fault to the victim. Customer service representatives comment upon the victim’s password hygiene when the loss is reported.
Yet the PIN lock is incongruent with a password defence. The compromised password has been changed by the victim upon discovery, so the password is no longer the issue.
Logic dictates that the vulnerability is not at the password.
Act 12: The Logical Breakdown
Through the “one time courtesy” refund, victims are led to believe their password was compromised and that they are at fault. Yet after discovery the password is changed. If the vulnerability were at the password, the PIN lock would be nonsensical: the fresh password would suffice.
The PIN lock exists because changing the password does not remove the attacker.
Act 13: The Proof at Your Desk
You can prove this yourself right now.
Log in to your Alaska account on two separate browsers.
Change the password on one browser.
Refresh the other.
You will still be logged in. Changing the password does not invalidate existing sessions. Anyone who holds a session cookie retains full access to the account regardless of how many password changes are made.
The session cookie does contain an expiry date. Unfortunately, that expiry is perpetually refreshed with each use, maintaining the session for as long as the attacker remains active.
If your account has been compromised and miles stolen, there is no point returning them. They will be stolen again, because the attacker’s access persists. There are two solutions: fix the system, or unplug the victim from it.
Alaska chose the latter. The fact that Alaska does not invalidate this token overwhelmingly suggests it cannot.
Act 14: Passwords Not Required
The most likely explanation is that the session token is stateless -- it is self-contained and not checked against a server-side session store. Without a revocation list (which Alaska does not appear to maintain), the server has no mechanism to invalidate it.
One could argue that the original sin remains: that the password was compromised and the victim is culpable. But that session cookie, the one that grants full account access, is readable by any script on the page.
The cookie is not marked HttpOnly. Nor does it carry other standard defences against exfiltration.
The HttpOnly flag has been a cornerstone of web security since 2008. Without it, every third-party script on the page can read the cookie’s contents, and most Chrome extensions have broad enough permissions to do the same. With that cookie, they have your account.
This investigation observed 14 outside companies with active cookies on Alaska’s authenticated pages. Those companies need not be malicious. If any one of them suffered a breach at any time, that breach could inject code to sweep up the session cookies of every Alaska member who logged in during the window of compromise.
It is not only these firms. Any attacker who can inject code into one of those 14 third parties, or into Alaska’s own site, gains the same access.
Even if a member’s password security is beyond reproach, the missing HttpOnly flag means most Chrome extensions with standard permissions can silently read the session cookie.
The full report contains further significant weaknesses in the architecture, but to bring it back to plain language: if anyone obtains this cookie, they gain a session with full account privileges. In testing, no secondary authentication was required to change email, phone number, or passport details. There appears to be no way to revoke their access. They follow your travels at every step.
Act 15: What Management Knows
It is inconceivable that management are unaware of this weakness after four years. For technical reasons described above, a compromised session cookie persists as long as the attacker keeps it alive. Hence the PIN lock: it is not a security measure for the customer but a containment measure for the vulnerability.
Instead of remediating the flaw, Alaska has blamed the customers, inconvenienced them, and sanctioned their accounts.
If management are genuinely unaware, they must provide a vigorous explanation as to how.
Act 16: The Bridge to Price
The main report identifies nine distinct factors detailing the impact upon the crown jewel of Alaska Air Group. Here it suffices to assert that these findings should have seismic implications for how consumers, partners, lenders, and investors value Atmos Rewards.
Act 17: The LinkedIn Mysteries Answered
The questions that drew the author into this investigation can now be answered with confidence.
Mystery 1: Why can Alaska not block these clearly fraudulent bookings and stop the thefts?
Because its systems cannot see them. The architecture that processes award redemptions has no fraud detection capability.
Mystery 2: What purpose could the mandatory telephone PIN booking forced upon the victim serve?
Compromised accounts remain compromised for as long as the attacker maintains an active session. Without the subterfuge of blaming the victim and forcing them into the telephone system, replenished accounts would be drained again immediately.
Mystery 3: Why would the fraudulent traveller take on such staggering risks?
Because flat-bed flights almost anywhere in the world are cheaper than a taxi to the airport. And law enforcement are, as a matter of policy, not informed of the thefts.
425 victims. An unknown multiple beyond.
A vulnerability unchanged for at least four years.
A front door that remains, today, wide open.
The full evidentiary report is available at https://noseyparker.pages.dev/baked-alaska